6 Tools for Hackers
#infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosec urity #cyberattacks #security #oscp #cybersecurity awareness #bugbounty #bugbounty tips


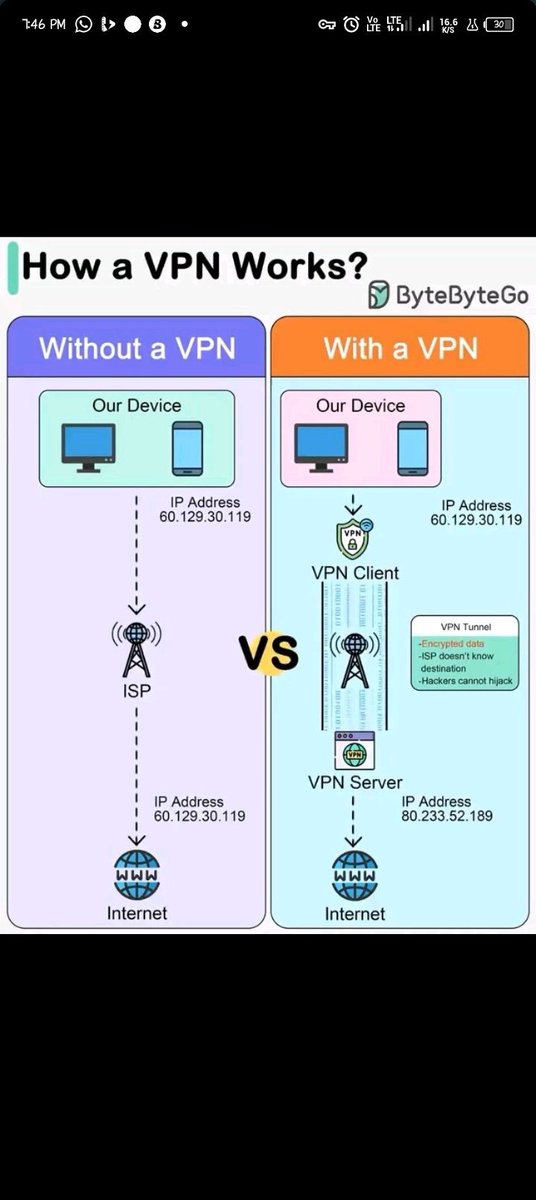
How a VPN Works? 🔥🔥📌
#infosec #cybersecurity #pentesting #redteam #VPN #networking #networksecurity #infosec urity #cyberattack s #Security #Linux #VPN works #cybersecurity awareness #httpstatus #bugbounty #bugbounty tips #attacks #cyberattack


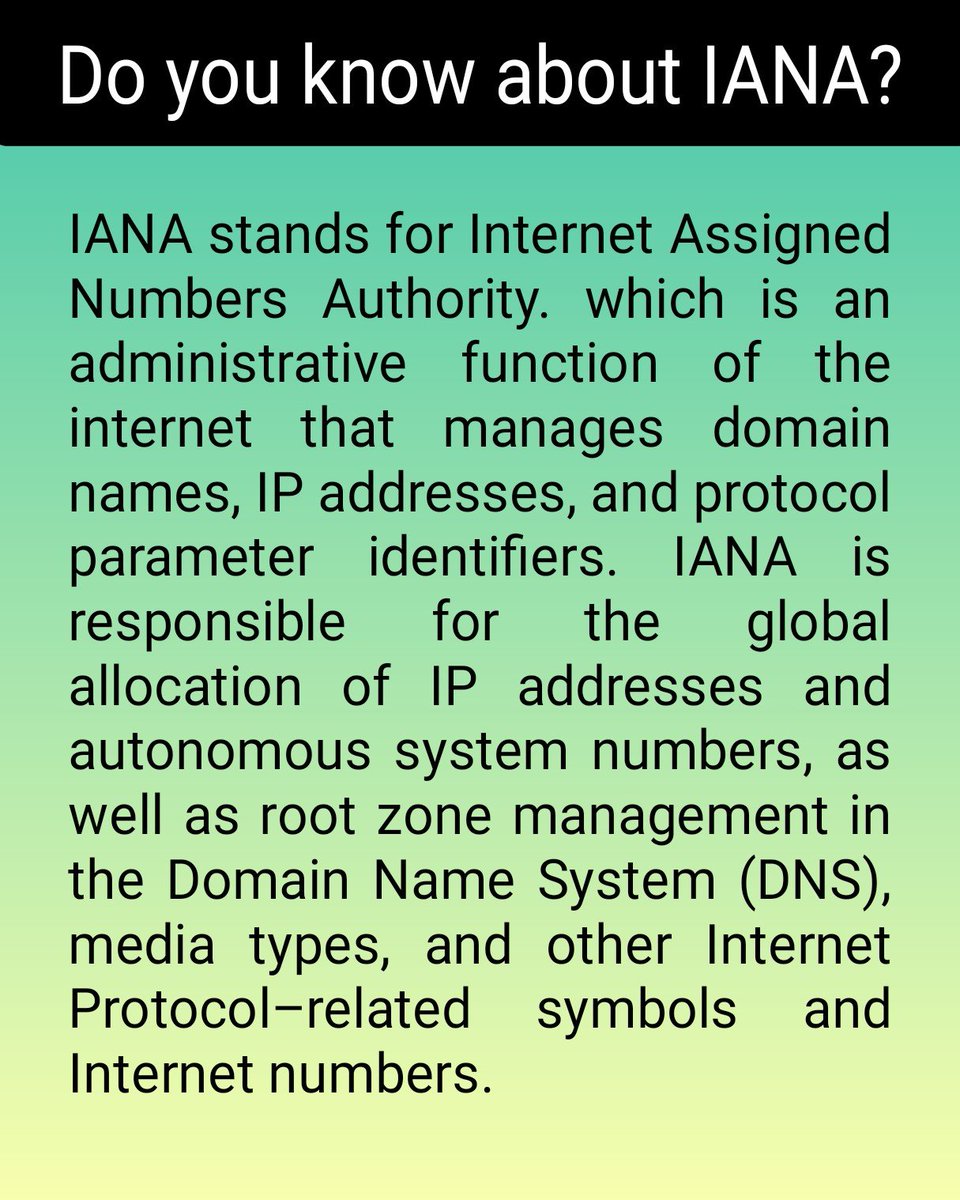
Do you know about IANA?
#networking #DoYouKnow #computer #Science #Engineering #networksecurity #progra

Alert Composer and Real-time Alerts
#Opinnate #NSPM #networksecurity #firewallrules #infosec #automation #policymanagement #cybersecurity #newpost

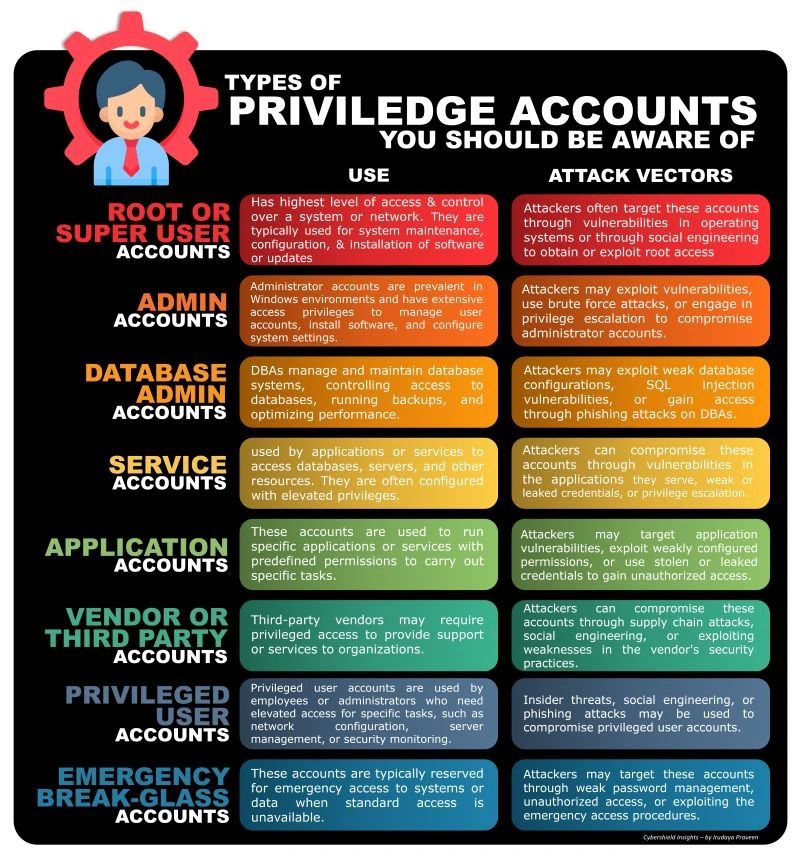
Types of Privilege Accounts
#infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosec urity #cyberattacks #security #oscp #cybersecurity awareness #bugbounty #bugbounty tips

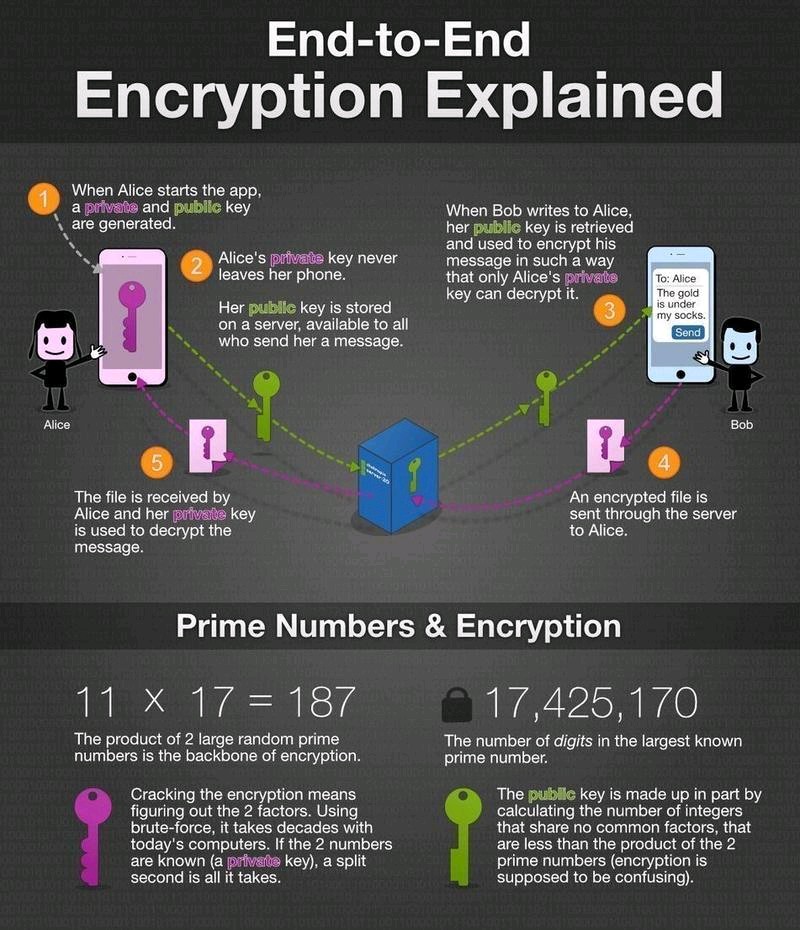
End to End Encryption
#infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosec urity #cyberattacks #security #oscp #cybersecurity awareness #bugbounty #bugbounty tips

Best of Cyber Security Tools
#infosec #cybersecurity #pentesting #oscp #informationsecurity #hacking #cissp #redteam #technology
#DataSecurity #CyberSec #Hackers #tools #bugbountytips #Linux #websecurity
#Network #Network Security #cybersecurity awareness #Devara



Implement essential strategies to safeguard your company's sensitive information. Learn more: ptt.technology/2024/05/06/wha…
#DataBreachPrevention #CyberSecurity #BusinessProtection #DataSecurity #IncidentResponse #NetworkSecurity #PerfectTimingHolding #PerfectTimingTechnologies


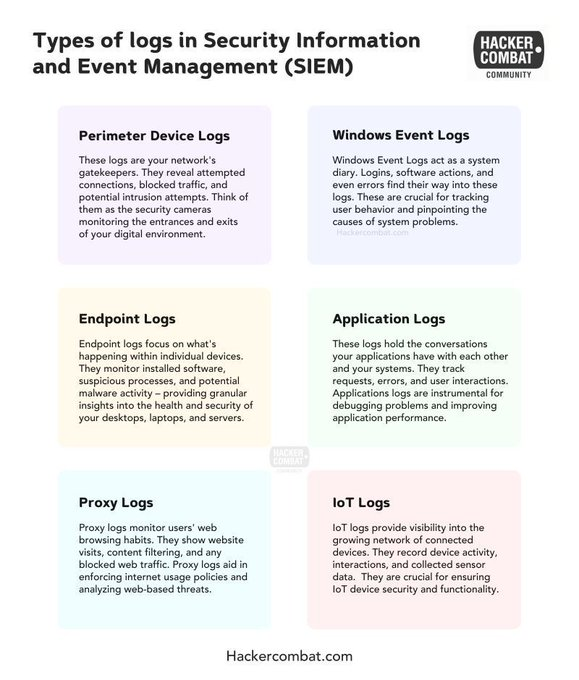
Types of logs in SIEM for SOC Teams
#infosec #cybersecurity #pentesting #redteam #VPN #networking #networksecurity #infosec urity #cyberattack s #Security #Linux #SIEM #SOCTeams
#SOCAnalyst #cybersecurity awareness #httpstatus #bugbounty #bugbounty tips #attacks #cyberattack

Forward Proxy vs Reverse Proxy
Credit: Bytebytego
#cybersecurity #pentesting #informationsecurity #hacking #technology #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

5 Best Practices in Monitoring IP Address Abuse
#monitoring #networkmonitoring #OnlineSafety #ThreatDetection #abuseprevention #digitalsecurity #cyberthreats #dataprotection #networksecurity #SecurityMeasures #securityawareness #ITsecurity
tycoonstory.com/5-best-practic…


Netoyed's advanced security solutions offer proactive defense and round-the-clock monitoring, ensuring the safety of your data, customer trust, and brand reputation. #networksecurity #CyberSecurityAwareness

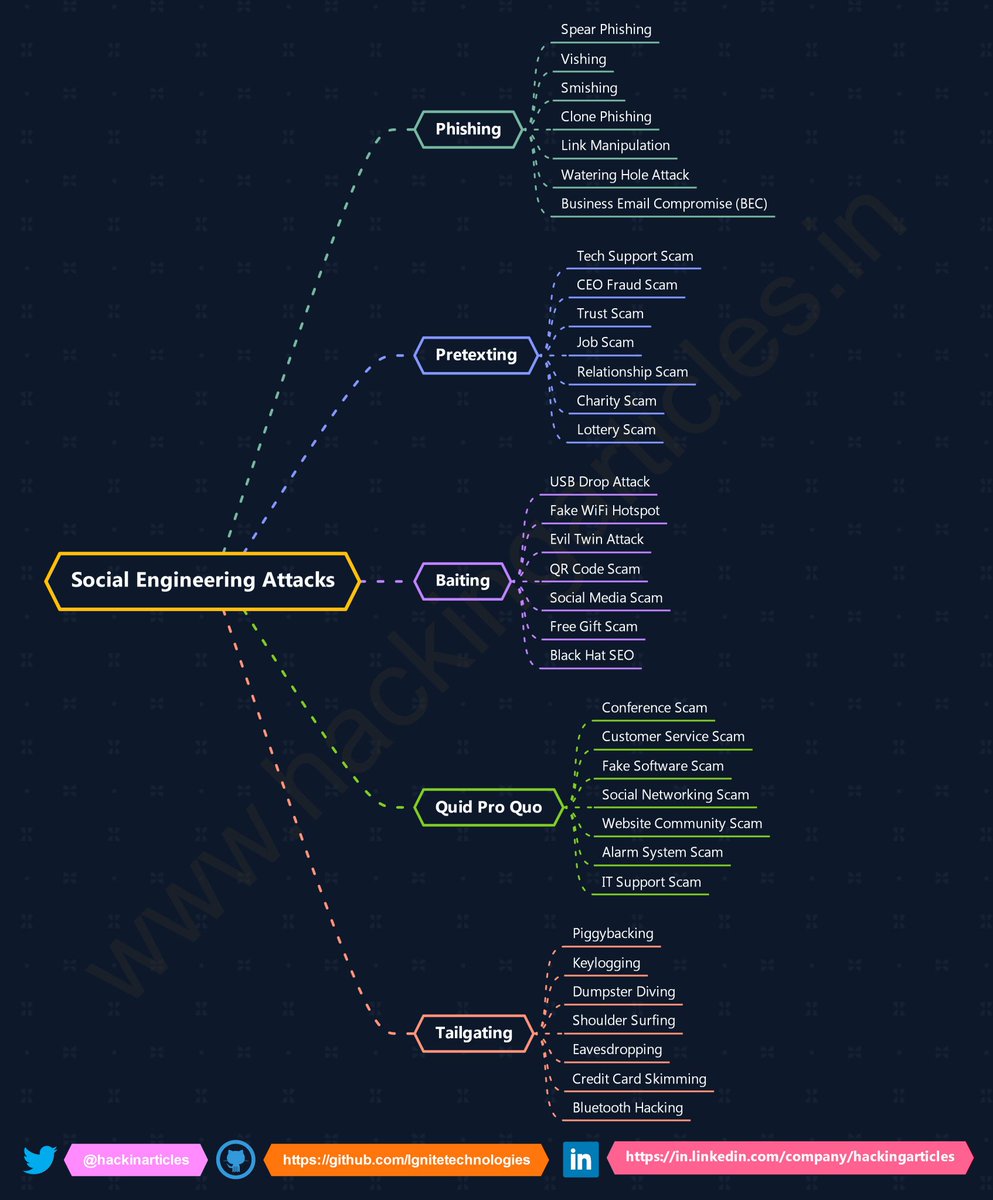
Social Engineering Attacks Cheat Sheet
#infosec #cybersecurity #pentesting #redteam #informationsecurity #CyberSec #networking #networksecurity #infosec urity #cyberattacks #security #linux #cybersecurity awareness #bugbounty #bugbounty tips

Forward Proxy vs Reverse Proxy
Credit: Bytebytego
#cybersecurity #pentesting #informationsecurity #hacking #technology #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness